For practitioners, in the Domain App report, you can isolate mobile apps by typing the following into the search box on the upper right of the page:
Android apps - type “com.” (notice the . after the com)
iOS apps - type “/id” (this is the syntax in Apple app store)
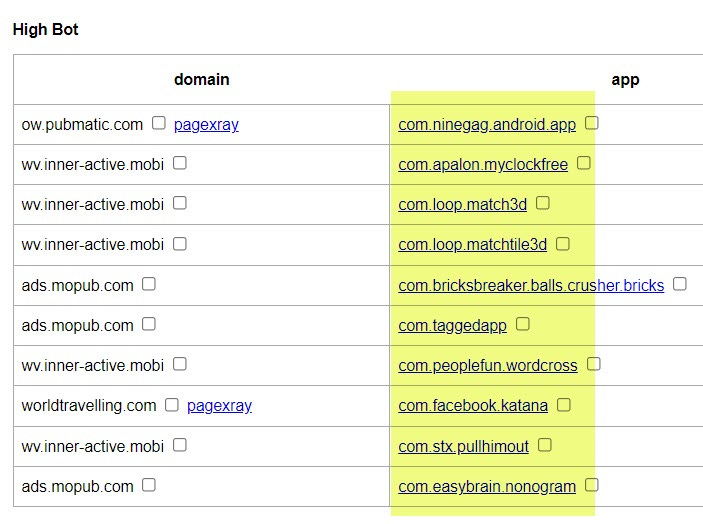
The screen shot below is for Android apps. Note the app name; the entry in the domain column to the left of each app name is the mobile exchange where the inventory came from. Also, each app is linked for you (blue links below) so you can click it and see it in the Google Play store to manually review the app. Look for strange developers (e.g. random gmail addresses), high ratios of reviews to downloads, and also age of the app)
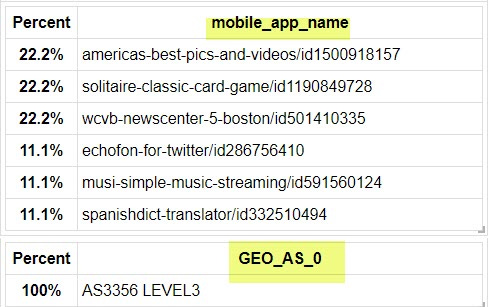
The screen shot below shows iOS apps. Again they are linked for your convenience so you can review them in the Apple app store.
Finally, when you dig into the apps that are listed under the “Fake Device” section of the Domain App report, you can also look for the name of the ISP. In the example below, you can see it is a data center (“Level 3”). That, combined with other factors, allows us to confirm it is a mobile emulator running the app so it can create more ad impressions 24/7. The apps that cheat in this way should be turned off as soon as possible.
Note the checkboxes next to the name of each app. Once you have reviewed these apps for cheating, you can check the checkbox and add them to the list of apps to turn off (add to block list). You find this list in the Executive Summary tab, in textareas so you can easily copy and paste the list and send to your agency to turn off.
Let me know if the above is helpful, and if you have any other questions related to finding apps that are being run by mobile emulators in data centers for ad fraud purposes.



I have a friend who is using cash app and told me to send money, but I saw suspicious activity and I feel like now he has my bank account number and routing numbers. He has an android and uses google go, but I can never really get his internet to work. Any suggestions